River Publishers Series in Communications and Networking
Identity Management for Internet of Things
Authors:
Parikshit Narendra Mahalle, Sinhgad Technical Education Society\'s, SKNCOE, Pune, India
Poonam N. Railkar, Sinhgad Technical Education Society\'s, SKNCOE, Pune, India
ISBN: 9788793102903
Available: January 2015
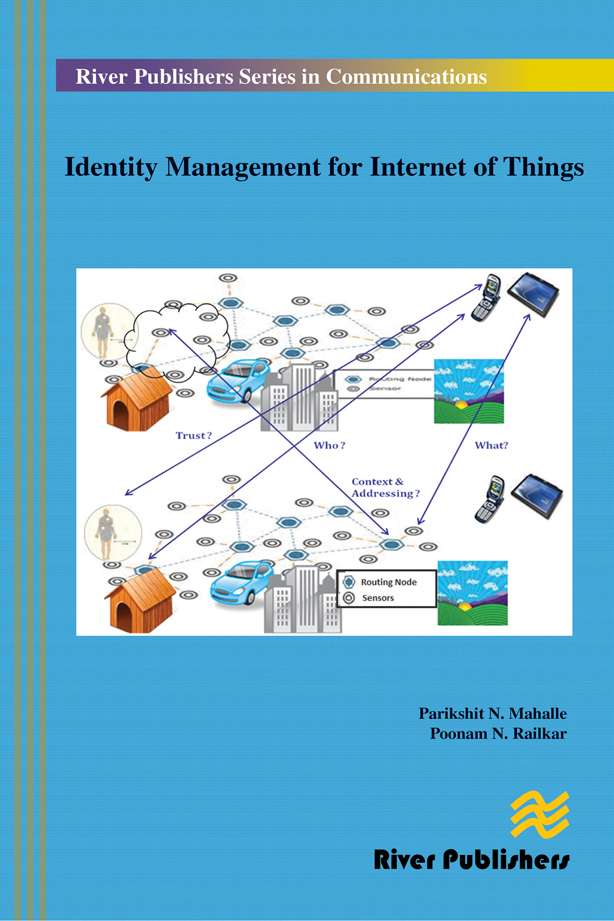
The Internet of Things is a wide-reaching network of devices, and these devices can intercommunicate and collaborate with each other to produce variety of services at any time, any place, and in any way. Maintaining access control, authentication and managing the identity of devices while they interact with other devices, services and people is an important challenge for identity management. The identity management presents significant challenges in the current Internet communication. These challenges are exacerbated in the internet of things by the unbound number of devices and expected limitations in constrained resources. Current identity management solutions are mainly concerned with identities that are used by end users, and services to identify themselves in the networked world. However, these identity management solutions are designed by considering that significant resources are available and applicability of these identity management solutions to the resource constrained internet of things needs a thorough analysis.
Technical topics discussed in the book include:
Identitymanagement for Internet of Things contributes to the area of identity management for ubiquitous devices in the Internet of Things. It initially presents the motivational factors together with the identity management problems in the context of Internet of Things and proposes an identity management framework. Following this, it refers to the major challenges for Identitymanagement and presents different identity management models. This book also presents relationship between identity and trust, different approaches for trust management, authentication and access control.Key milestones identified for Identitymanagement are clustering with hierarchical addressing, trust management, mutual authentication and access control.
Identitymanagement for Internet of Things is ideal forpersonnel in computer/communication industries as well as academic staff and master/research students in wireless communication, computer science, operational research, electrical engineering andtelecommunication systems Internet, and cloud computing.